KubeCon EU 2022 in Valencia

Last week me, and a couple of ITQ colleagues, Robert Kloosterhuis and Michael Van de Gaer went to Kubecon EU 2022 in Valencia. In this post I will be sharing my thoughts, experiences and, at the very bottom, I add some of my favourite sessions.
It might be worth mentioning that I am from Valencia, so having this amount of people with shared interests in the city felt amazing. Not to forget that I also could show Valencia and share my culture with my colleagues and some of my partners, such as Scott Rosemberg (Terasky) and Steve Wong (VMware).
GitOpsCon
On Tuesday we joined GitOpsCon, one of the CNCF collocated events. According to the GitLab website, GitOps is an operational framework that takes DevOps best practices used for application development such as version control, collaboration, compliance, and CI/CD, and applies them to infrastructure automation.
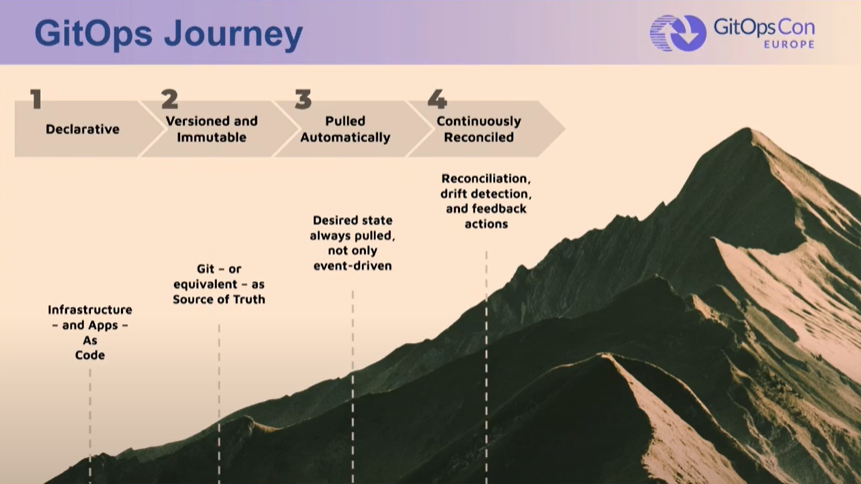
There are four main principles in GitOps, which can also be seen as a ladder, or a journey:
- Declarative
A system managed by GitOps must have its desired state expressed declaratively. - Versioned and Immutable
Desired state is stored in a way that enforces immutability, versioning and retains a complete version history. - Pulled Automatically
Software agents automatically pull the desired state declarations from the source. - Continuously Reconciled
Software agents continuously observe actual system state and attempt to apply the desired state.
source: OpenGitOps.dev
KubeCon
The booths we visited
We spent quite some time around the VMware booth, chatting with some of the VMware partners we already knew, meeting new ones, and also getting to know some of the people behind Tanzu TV.

Aside from that, I don’t think I could possible remember all the booths we visited, but I am gonna try: ArgoCD, Cert-Manager, InfluxDB, Komodor, Giant Swarm, Knative, Runecast, HashiCorp, MinIO, Datadog, Rancher, AWS, Trend Micro and ELOTL.
I am not gonna lie, with this being my first conference, I did not realize how fast time passes, and even though those are not all the booths we visited, I can think about a few of them that I did not have time to visit. I guess next year I will have to be more strategic with my time.
Products I will (immediately) be looking into
I left KubeCon with a ton of homework. Since I obviously have to prioritize, I will now go through the main tools I will be learning soon and then give a special mention to other ones that will have to wait a bit before I start getting into them.
ArgoCD
ArgoCD was one of the most popular tools during the whole KubeCon, and it is a tool that, up to last week, still had not look into. So, we went to the booth, and were lucky enough to get an overview of ArgoCD from Dan Garfield, the co-founder of Codefresh and one of the main people behind the ArgoCD project. Unfortunately for us, with ArgoCD being such a popular tool, we were not able to score a t-shirt.

As I understand, ArgoCD works mainly by deploying application controllers, which continuously monitors running applications and compares their current state with the desired one, and “synchronizes it”. Additionally, it will invoke user-defined hooks for lifecycle events.
For more information, check out the ArgoCD website.
Tekton
According to Tekton’s website, Tekton is a powerful and flexible open-source framework for creating CI/CD systems, allowing developers to build, test, and deploy across cloud providers and on-premise systems.

Tekton allows you to automate your deployments by creating tasks that can run within pipelines, both being Kubernetes CRDs that Tekton will manage. Additionally, triggers can be used to instantiate pipelines based on events.
It is also worth mentioning the existance of Tekton Hub, a web UI used to access the Tekton Catalog, which is a repository of community-contributed Tekton building blocks that are ready for you to use in your own pipelines. I have already been looking at some of the tasks at Tekton Hub, and how they are built, and all I can say is that I will for sure be submitting some tasks or pipelines to it as I gain more Tekton experience.
Even though I have spent time in the last months learning another CI solution, Concourse, and perhaps about 4-6 hours in Tekton, I can already see some of the advantages Tekton can offer over Concourse. The sole fact of it being Kubernetes native, and just being able to easily feed it values from secrets or configmaps is a big plus.
Additionally, I think community adoption and traction are key when deciding which building blocks you will be using for constructing your cloud-native platform or environment, and Tekton’s project seems to only be growing while there is very little activity in the Concourse CI project.
Cert-Manager
I am tired of dealing with self-signed certificates, and I am sure so are you. Unless you are already using Cert-Manager, which I am starting to explore. According to their website, Cert-Manager is a Kubernetes native solution, which adds certificates and certificate issuers as resource types in Kubernetes clusters. It can issue certificates from diverse sources such as Let’s Encrypt or HashiCorp Vault, among others.
Cert-Manager is one of the main packages in Tanzu Kubernetes Grid and Community Edition, and even though I have already installed it, and it is being used by other Tanzu packages, I have not used it outside of Tanzu yet. In the coming weeks I will learn how to create and manage certificates with Cert-Manager, and will for sure be blogging about it.
Tanzu Application Platform
Last but not least, is Tanzu Application Platform. Shortened as TAP, Tanzu Application Platform is a GitOps based, modular, application-aware platform that aims to improve developer experience and productivity.
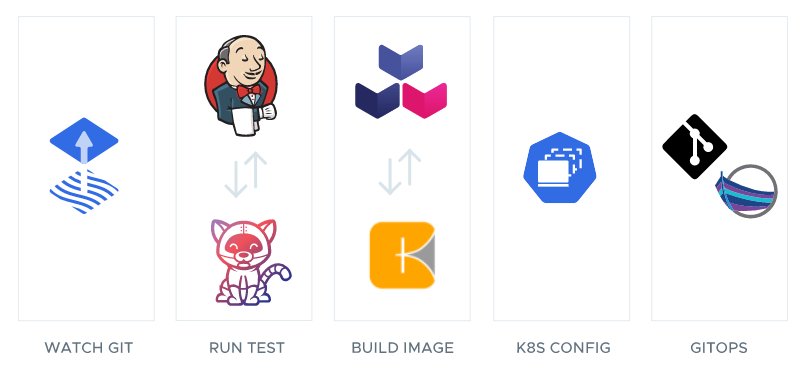
TAP is built with open source components, and it takes care of the whole supply chain for your application. Under the hood, uses FluxCD to watch Git; Jenkins or Tekton for Running tests; Buildpacks.io for building the images; Kubernetes config as config source; and Carvel and Git for implementig GitOps. It also uses Cartographer, which allows App Operators to create pre-approved paths to production by integrating Kubernetes resources with their existing toolchains.
Even though TAP is not open source, VMware did release an open source version of it, called App Toolkit, which you can deploy as a package in Tanzu Community Edition.
Special mentions
As I said before, there are some other products I would like to explore, such as Knative, Cillium, FluxCD, Backstage, Buildpacks.io, Cartographer or Crossplane, but since there are only so many hours in a day, they will have to wait! Nevertheless, since some of these are core components of Tanzu Application Platform, I will for sure be learning a bit more about them soon.
Additionally, there was also some propietary software which I also found interesting, such as Komodor, for automating Kubernetes troubleshooting, and Datadog, for full-stack observability. These two products are SaaS based, and offer a two week trial.
Evening events & dinners
Tuesday: Google Partner dinner

On Monday, after getting our badges and spending the day showing Valencia to Robert and Michael, we joined the Google Partners dinner. We ate at the Basque restaurant Sagardi, where we had some fantastic red wine and a massive Txuleton (see pic). During the meal I got to meet some Google engineers from all over the world and to learn more about what other Google Partners, such as Jetstack (the company behind Cert-Manager) and Devoteam are doing, as well as hearing stories from the former project manager for Youtube for TV (yes, the app in smart TVs). The dinner was, all in all, a great evening. You could say it was the appetizer for what was to come during the rest of the KubeCon week.
Wednesday: VMware user group Dinner
We had the chance to get together with some of the people behind Tanzu Community Edition at the VMUG Dinner. Invited initially by Steve Wong, I was sitting in a corner of the table with Scott, John McBride and David vonThenen, two of the mantainers for the TCE. I loved talking with them about the beginnings of Pivotal and how the industry got to Kubernetes, and the flexibility it offers as opposed to other platforms that already existed at the time, such as Heroku or Cloud Foundry. It also blew my mind to hear how John is a single mantainer for Cobra (Go Library used in many CLI tools such as Kubectl, Helm and Terraform, among others). You can read more about this, and some of Scott’s opinions in his latest blogpost for Terasky.
Wednesday: Palo Alto Networks / Snyk party at Umbracle
For this we have to thank Scott Rosenberg, who let us know about this event a few hours in advance. Snyk and Palo Alto Networks rented Umbracle (probably the best venue in Valencia) for their own private party. In here, Michael ran into some former colleagues, who recently founded a DevOps startup in Belgium, called OKKO. We spent most of the night drinking and chatting with them, in this very stunning venue.

Thursday: All-Attendee Party (sponsored by Kasten + Snyk) at Masia Aldamar
On Thursday evening, a fleet of buses picked all KubeCon attendees and took us to Masia Aldamar, in the municipality of Chiva. This was a great event, with diverse food stations such as BBQ, sushi, and of course, a massive paella.
In this event I ran into Nico Vibert, Senior Technical Marketing Engineer at Isovalent, the company behind Cillium. I first encountered Nico’s blog at the begining of my time at ITQ, about a year ago, when he was still working at VMware. Through Nico’s blog I learnt a lot of Terraform, and when I saw him at this event, I stopped him to thank him for all his great content. After he went on to explain what eBPF is all about and a what he is currently doing at Isovalent. I was surprised to find out that Nico did his Erasmus studies in Valencia, so we also had the opportunity to exchange some experiences about the city and Valencian culture, which I must say, he knew a lot of.

Last thoughts
Before going to KubeCon, I already knew that it would be great for my learning and development, but now I actually realized the importance of going to an event like this. The possibility of learning about so many different products, as well as the networking aspect of it, makes going to these kind of events crucial, so you will for sure be seeing me again.
I have personally spent a lot of time in the last year in the technical bits of Kubernetes and Tanzu, but the talks, and the conversations we had with people, opened my eyes to the fact that technology is almost worthless if you do not give it a context, and if you don’t really understand what problem it is trying to solve. I think at ITQ we know that very well, thats why we “love technology but are obsessed with our partner’s success”.
KubeCon EU 2023 in Amsterdam

From my favourite city in the world, to my second faviourite city and current residence, KubeCon EU is coming to Amsterdam next year! I was very excited to hear that KubeCon is comming to the Netherlands next year, because, once again, I get the chance to show my city to all my new KubeCon friends.
BONUS: Highlighted sessions
As of the date of the publishing of this blogpost, only the GitOpsCon sessions are available in Youtube. As soon as the KubeCon sessions are uploaded, I will be adding a bunch more into the list below.
So, that was it, all I am left to say is …
…
SEE YOU NEXT YEAR!


